All content
Browse all articles and insights from the TrueScreen blog
Articles

Document dematerialization: from scanning to legally certified digitization
Complete guide to document dematerialization: from scanning to legally certified digitization with blockchain timestamping.

Advanced Electronic Signature: What It Is, How It Works, and eIDAS Regulation
Advanced electronic signature (AES) under eIDAS: the 4 requirements, legal validity across EU, and how to integrate AES in business workflows.

Social Media Evidence in Court: How to Capture and Authenticate Posts
Learn how to capture and authenticate social media posts for court. Forensic methods, FRE 901 requirements, and preservation tools compared.

FRE 901: How to Authenticate Digital Evidence Under Federal Rules
FRE 901 requires evidence sufficient to support a finding of authenticity. Complete guide to all 10 authentication methods, Rule 902, and proposed 901(c).

Video Evidence with Altered Timestamps: Court Admissibility Standards
How courts evaluate video evidence with modified timestamps. Forensic authentication standards, metadata analysis, and legal precedents for admissibility.

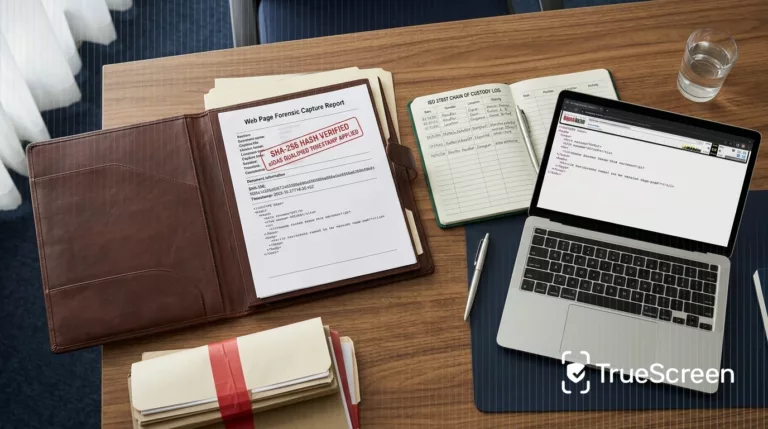
Digital Chain of Custody: What It Is and How It Protects Evidence
Digital chain of custody: what it is, ISO 27037 requirements, and how forensic acquisition protects evidence integrity from capture to court.

Screenshot Evidence in Court: How to Make Screenshots Legally Admissible
Plain screenshots are rarely admissible. How to authenticate them under FRE 901 and eIDAS, with technical steps to make evidence defensible.

Court-Ready Blockchain Evidence: Legal Standards and Admissibility
How to make blockchain evidence admissible in court. FRE 901 authentication, chain of custody, forensic certification, and eIDAS compliance for litigators.

How to Preserve Digital Evidence for Court: The Complete Guide
Digital evidence preservation follows ISO 27037 4 phases. Learn chain of custody, forensic certification and common mistakes that cause evidence exclusion.

Photo Verification: How to Verify and Authenticate Digital Images
Photo verification methods explained: EXIF analysis, reverse search, ELA and their limits. Why certification at source beats post-hoc detection.

The digital trust gap: why every piece of data will need a trust layer
The digital trust gap is widening as AI-generated content outpaces verification. A trust layer certifies data authenticity at source, not after the fact.

The litigation cost of uncertified evidence: when a judge rejects a photo
Uncertified digital evidence costs denied claims, forensic fees and months of delay. What happens when a judge rejects a photo and how to prevent it.

How to Certify Photos with Legal Value: A Forensic Guide
When is a digital photo admissible as evidence in court? Legal standards, chain of custody, qualified timestamps, and what judges actually look for.

AI fingerprints can be removed and forged: the Edinburgh study that challenges deepfake detection
Edinburgh researchers tested 14 fingerprinting methods on 12 AI generators. Result: 80%+ removal, 50%+ forgery success. Why digital provenance beats.

eIDAS 2 and Qualified Electronic Seals: What Changes for European Businesses
Qualified electronic seals under eIDAS 2 Regulation (EU 2024/1183): QTSP requirements, EUDI Wallet deadlines, and compliance steps for European businesses.

Document Forgery in the Age of AI: Risks, Real Cases and How to Protect Yourself
Generative AI has made document forgery accessible to anyone. Analysis of AI fraud techniques, real cases, regulatory framework and source certification.
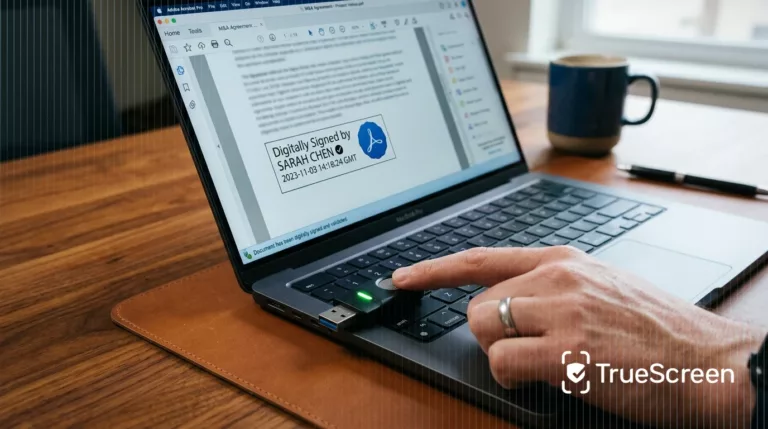
Digital Signature: Practical Example, How It Works and How to Verify It
Practical example of a digital signature on PDF documents. Learn how it works, the difference between CAdES, PAdES and XAdES, and how to verify validity.

Data Certification for AI Agents: Governance, Compliance and Legal Liability
Agentic AI governance requires data certification at 4 levels. Legal framework, AI Act art. 12 compliance and audit trail.

C2PA Standard: History, Promises and Structural Limitations
C2PA standard explained: technical architecture, adoption by Google and OpenAI, structural limitations from metadata stripping to trust gaps, and why forensic methodology fills the gap.
Electronic Seal: What It Is, How It Works, and Differences from Digital Signature
The electronic seal certifies data origin and integrity for legal entities. Technical architecture, eIDAS levels, and differences from digital signatures.
Insights
Hash SHA-256 and qualified eIDAS timestamping: the forensic language every law firm should master

Voice cloning CEO defense: stopping BEC 2.0 with source-certified corporate audio

Work progress photo evidence: building site documentation that holds up in appellate court

Storm 1516: anatomy of Russia’s AI disinformation machine in 2026

How to timestamp a document: practical guide and method comparison
B2B formal demand: how to prove emails, registered delivery and screenshots in court

Certifying audio recordings as court evidence: chain of custody and qualified timestamp

Remote-work information notice: how to prove delivery and meet EU compliance

Content provenance in newsrooms: a six-step verification workflow

WhatsApp stalking evidence: digital proof after Italian Supreme Court ruling 6024/2026

Deepfake video and biometric KYC bypass: defending bank onboarding in 2026

Certified digital whistleblowing reports: balancing evidence and anonymity under the EU Directive

Video Evidence in Private Investigations: Admissibility in Civil and Criminal Proceedings (2026)

Chain of custody of digital evidence: operational guide for lawyers and law firms

Corporate Espionage: How to Document Trade Secret Theft with Court-Ready Digital Evidence

Mortgage property appraisal: what lenders look for and what evidence you need in 2026

Screen recording in remote work: how to protect employees and employers with certified digital evidence
Certified Web Evidence vs Wayback Machine: Three Evidentiary Scenarios

AI Act Article 50: EU Rules on Labelling Synthetic Content from 2 August 2026

