Latest articles
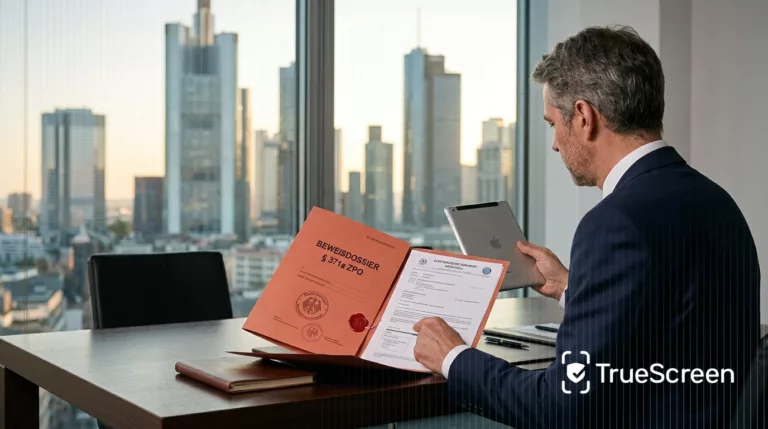
Digital evidence in German civil procedure: chain of custody under § 371a ZPO and eIDAS
Verbatim explainer of § 371a ZPO, eIDAS Article 25, GoBD and Beweiskette: how digital evidence holds up in German civil and criminal courts.

How chain of custody for digital evidence works in UK proceedings
How chain of custody for digital evidence works under ACPO Principle 3, CPR Part 31 and Practice Direction 31B in UK courts and tribunals.

Image authentication for enterprises: the four levels that secure your visual assets
Enterprise image authentication explained: the four operational levels, when each is required, and how to embed them in document workflows beyond AI.

Voice cloning corporate fraud: the verifiable defense for CFOs after the Arup case
After the Arup 25.6M deepfake fraud, voice cloning targets corporate finance: the defense for CFOs with certified voice baseline and out-of-band rules.
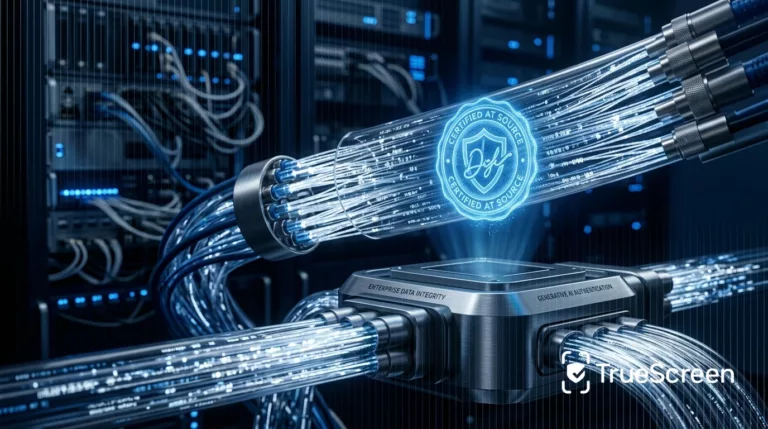
Data integrity in the AI era: why source certification rewrites the paradigm
Classic data integrity falls short in the generative AI era. Source certification extends the guarantee to the moment data is born.

EU e-Evidence Regulation for Service Providers: Obligations, Orders, and Cross-Border Cooperation
Insights

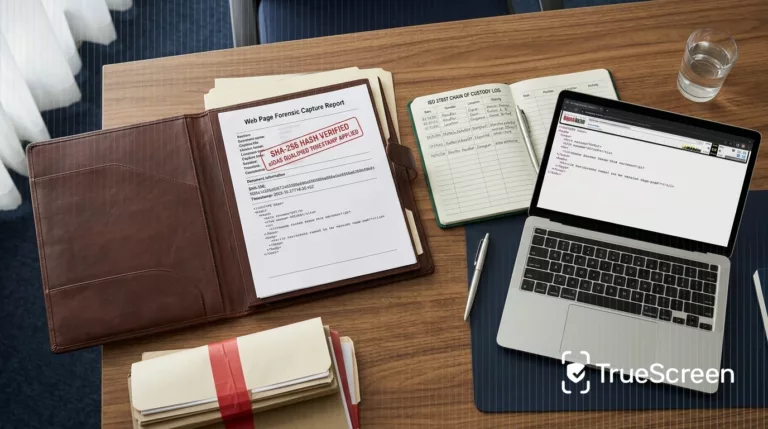
Corporate Espionage: How to Document Trade Secret Theft with Court-Ready Digital Evidence

Mortgage property appraisal: what lenders look for and what evidence you need in 2026

Screen recording in remote work: how to protect employees and employers with certified digital evidence