All content
Browse all articles and insights from the TrueScreen blog
Articles

eIDAS 2 and Qualified Electronic Seals: What Changes for European Businesses
Qualified electronic seals under eIDAS 2 Regulation (EU 2024/1183): QTSP requirements, EUDI Wallet deadlines, and compliance steps for European businesses.

Document Forgery in the Age of AI: Risks, Real Cases and How to Protect Yourself
Generative AI has made document forgery accessible to anyone. Analysis of AI fraud techniques, real cases, regulatory framework and source certification.
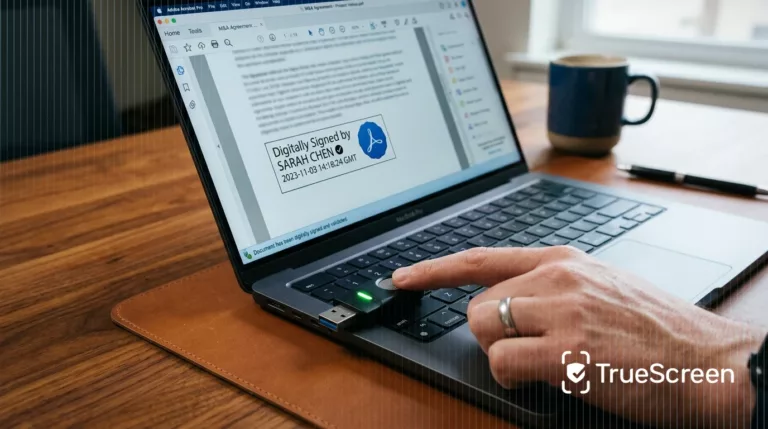
Digital Signature: Practical Example, How It Works and How to Verify It
Practical example of a digital signature on PDF documents. Learn how it works, the difference between CAdES, PAdES and XAdES, and how to verify validity.

Data Certification for AI Agents: Governance, Compliance and Legal Liability
Agentic AI governance requires data certification at 4 levels. Legal framework, AI Act art. 12 compliance and audit trail.

C2PA Standard: History, Promises and Structural Limitations
C2PA standard explained: technical architecture, adoption by Google and OpenAI, structural limitations from metadata stripping to trust gaps, and why forensic methodology fills the gap.
Electronic Seal: What It Is, How It Works, and Differences from Digital Signature
The electronic seal certifies data origin and integrity for legal entities. Technical architecture, eIDAS levels, and differences from digital signatures.

Content Authenticity: Why Certification at Source Is the Only Scalable Defense
Content authenticity and digital provenance: why AI detection fails systematically and how forensic certification at source protects enterprises.

AI war disinformation: why certified evidence beats detection
18 false claims in three weeks. AI detection tools cannot keep up. Forensic content certification at capture is the proven alternative for conflict zones.
Qualified electronic timestamps: how they work and when they are legally required
What qualified electronic timestamps are, how they work under eIDAS, and why the legal presumption of accuracy matters for digital evidence.

Real estate deepfake fraud and forged documents: how to protect transactions
Real estate scams with deepfakes and forged documents: wire fraud risks for buyers and sellers, and how forensic certification protects every transaction.

Deepfake detection: why it fails at scale and what data authenticity platforms do instead
Deepfake detection accuracy drops below 40% on unseen models (NIST). Data authenticity platforms certify content at the source with forensic methodology.

Digital forensics certification: what it means to certify data with forensic standards
Digital forensics certification explained: international standards, forensic acquisition methodology, and chain of custody for court-admissible evidence.
Digital evidence in insurance: how to protect the claims process from AI manipulation
Digital evidence in insurance claims is vulnerable to AI manipulation. Forensic source certification guarantees integrity and legal validity of every.

Data provenance: tracking data origin, lineage, and source authenticity
Data provenance tracks where data comes from. Data lineage tracks where it goes. The differences, why source authenticity matters for AI, and how to verify...

Digital Provenance: Definition, Tracking, and Trust in the AI Era
Digital provenance proves where data comes from and how it changed. Definitions, standards, and certification methods for authentic content.

How to Make Digital Evidence Admissible in Court (2026)
What makes digital evidence admissible in court: ISO 27037, chain of custody, authenticity tests, and forensic certification methods.

ECGT Directive: Why Corporate Environmental Data Must Be Certified
The ECGT Directive requires companies to certify environmental claims with verifiable data. Compliance requirements, timelines, and penalties explained.

Insurance fraud in the generative AI era: why certifying evidence is the only structural defense
AI-generated insurance fraud costs $308 billion a year. Why detection is not enough and how forensic evidence certification changes the rules.

Web page certification: how to obtain digital evidence with legal value
Web page certification turns online content into legally valid evidence. Screenshot limits, alternatives, and forensic methodology explained.

How to certify an email: complete guide to email certification
Email certification preserves content, sender and date with a digital signature and qualified timestamp, creating eIDAS and ISO 27037 compliant evidence.
Insights

Due Diligence and Remote Negotiations: Certifying Commercial Discussions

Online Corporate Assemblies: How to Certify Remote Resolutions

Zoom, Teams, Meet: Certify Video Calls on Any Platform

Certified Screen Recording: How the Digital Chain of Custody Works

Recording a Meeting Without Consent: Legality, Limits and GDPR

